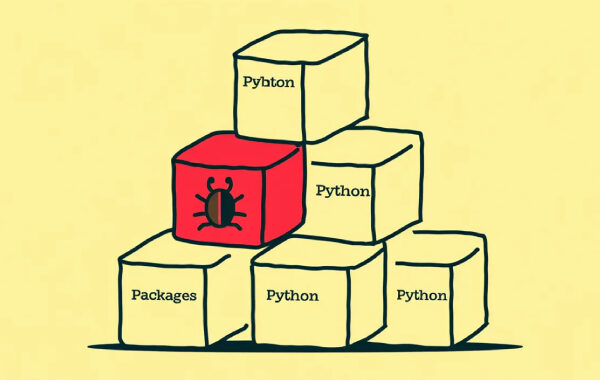
Malicious Python Packages on PyPI Downloaded 39,000+ Times, Steal Sensitive Data
Cybersecurity researchers have uncovered malicious libraries in the Python Package Index (PyPI) repository that are designed to steal sensitive information. Two of the packages, bitcoinlibdbfix and bitcoinlib-dev, masquerade as fixes for recent issues detected in a legitimate Python module called bitcoinlib, according to ReversingLabs. A third package discovered by Socket, disgrasya, contained a